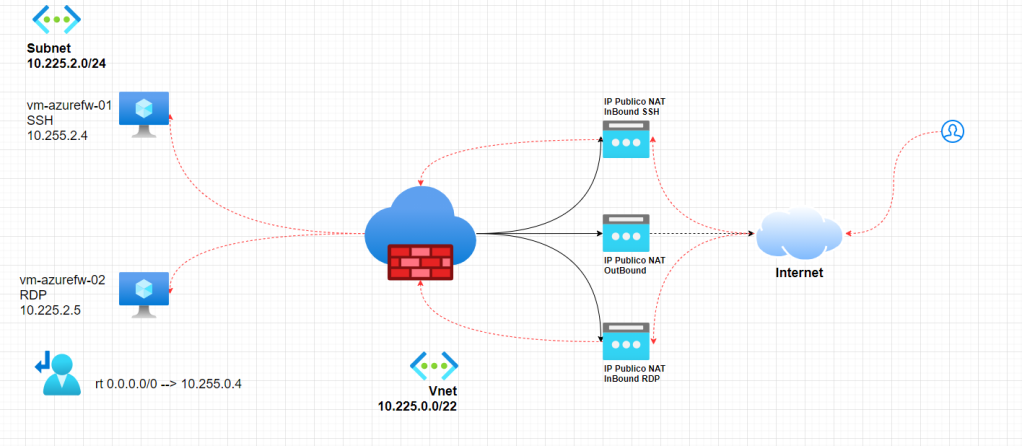
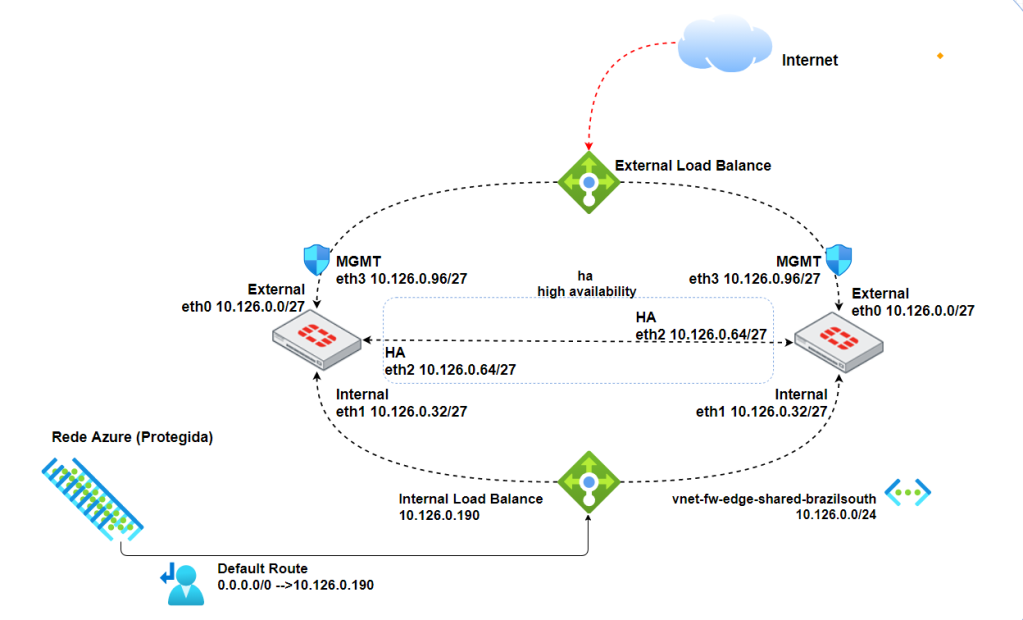
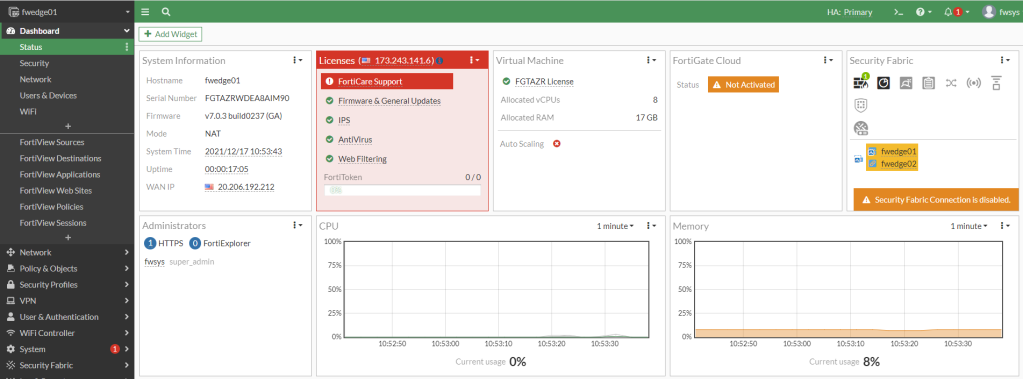
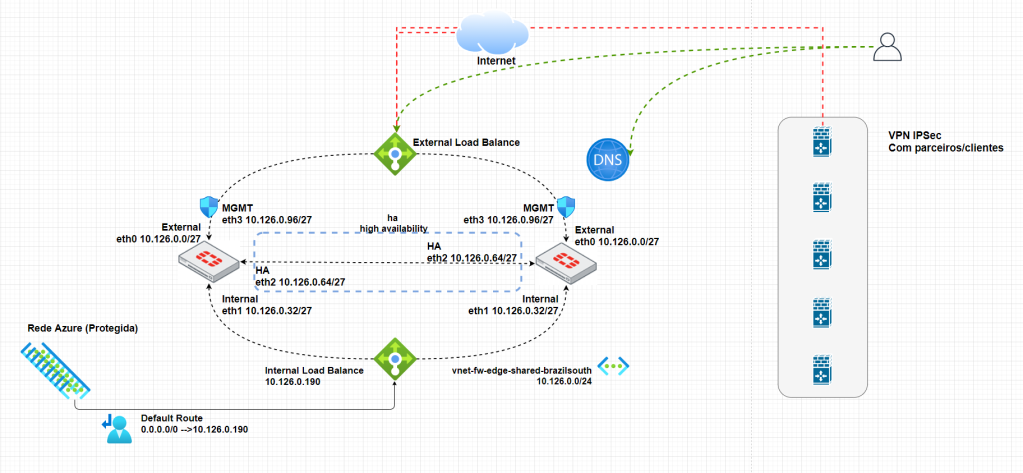
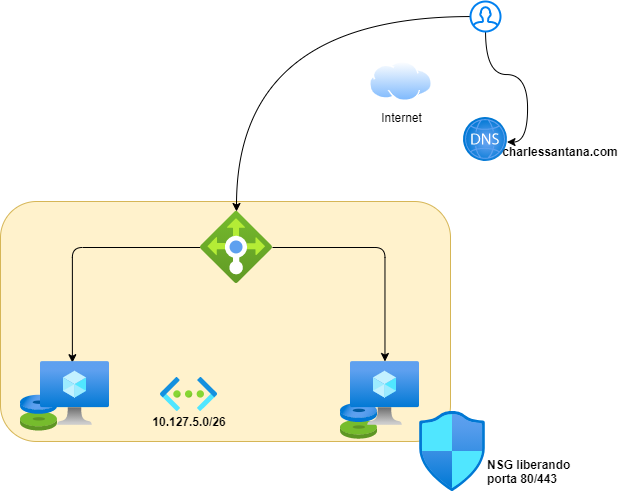
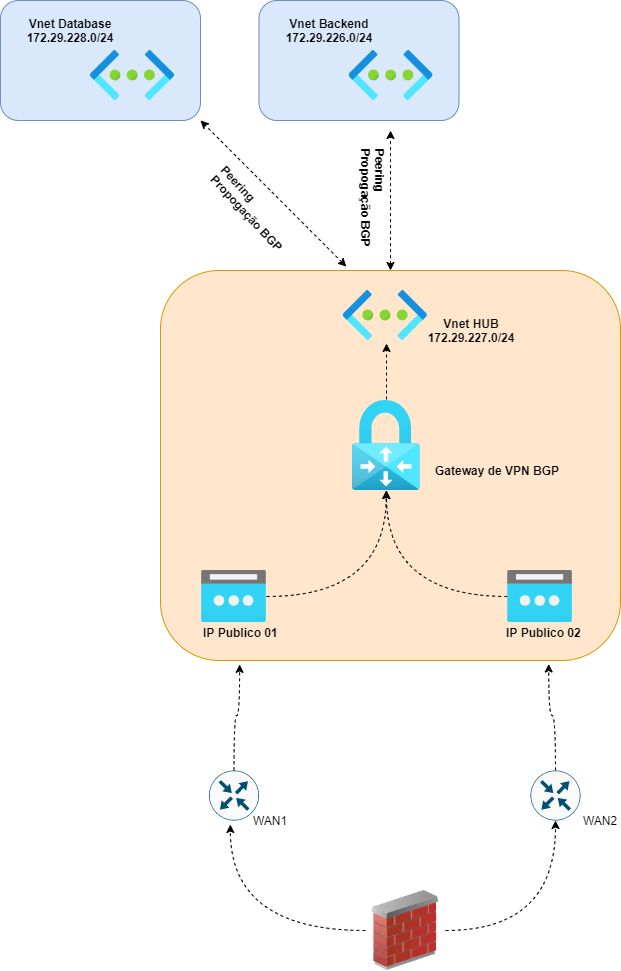
Olá, neste post iremos fazer o deploy do Azure Firewall em uma infraestrutura de Firewal EDGE (como ja feito com Palo Alto e Fortigate)
Nesta topologia teremos Azure Firewall como borda de toda rede Azure (neste exemplo)
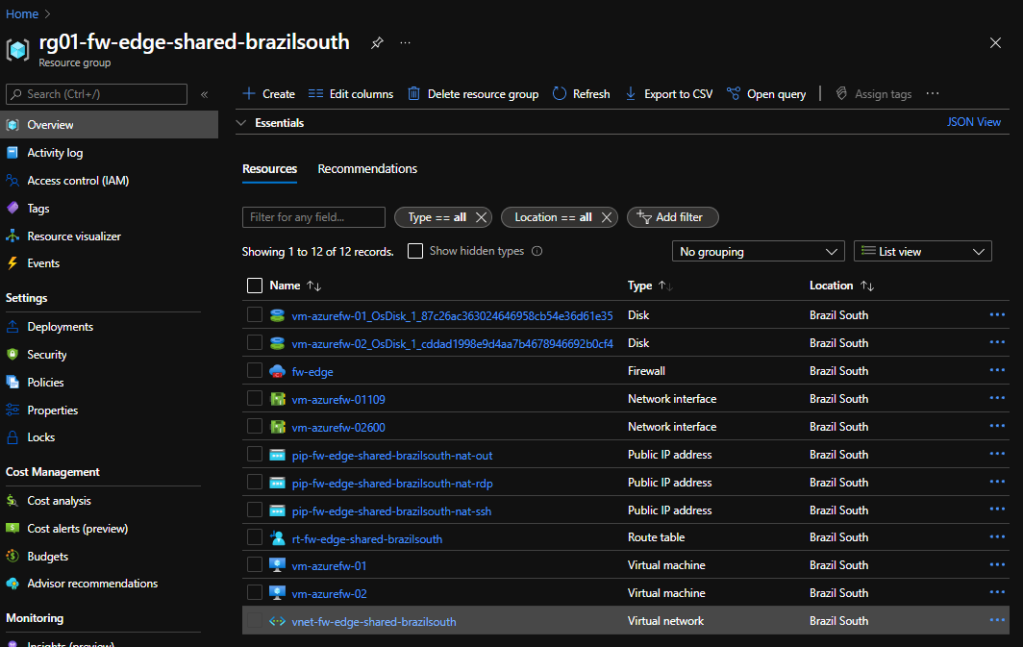
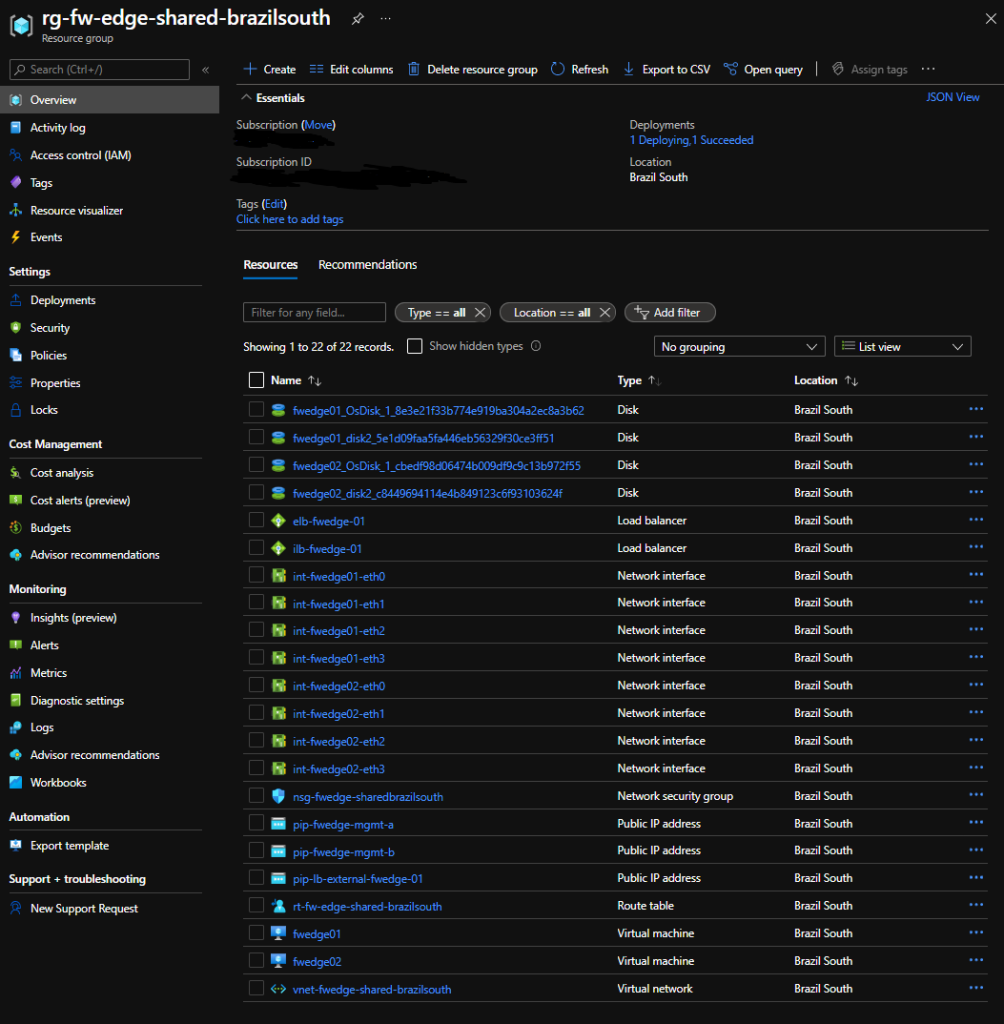
Vamos aos objetos criados
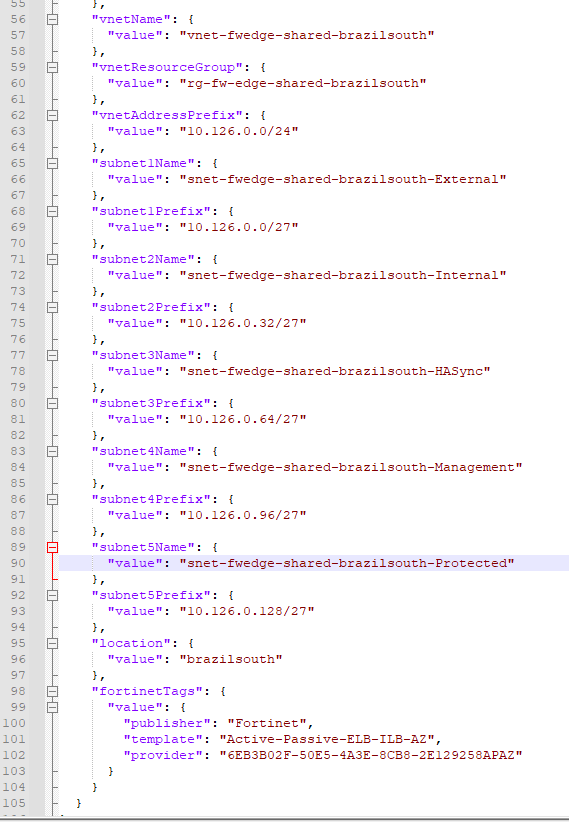
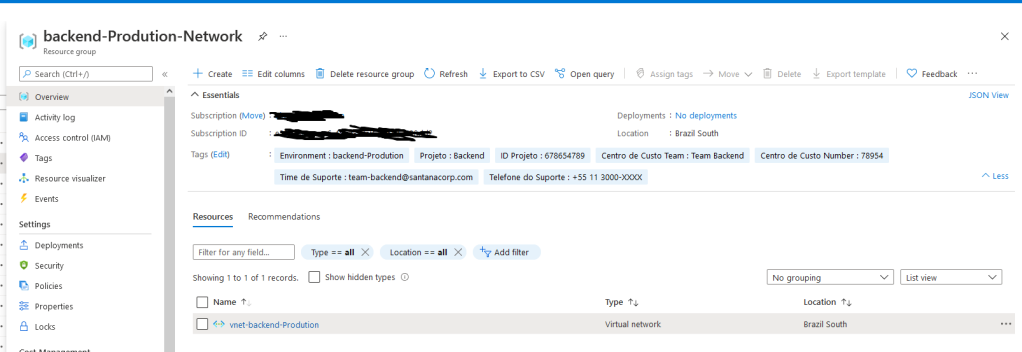
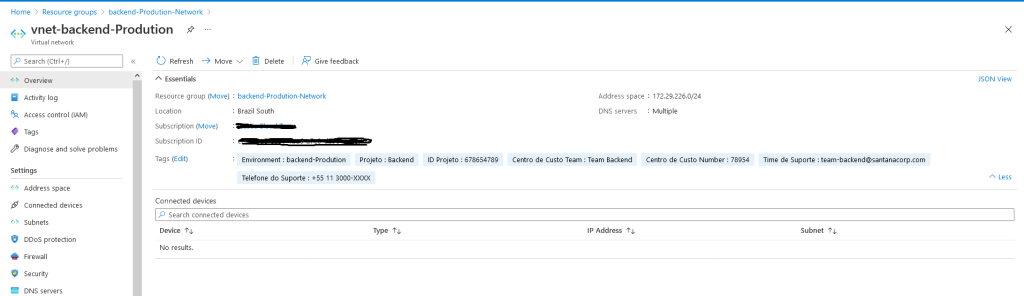
| Objeto | Name | Descrição |
| Resource Group | rg01-fw-edge-shared-brazilsouth | RG |
| Azure Firewall | fw-edge | Standard |
| Public IP | pip-fw-edge-shared-brazilsouth-nat-out | xxx.xxx.xxx.xxx |
| Public IP | pip-fw-edge-shared-brazilsouth-nat-rdp | xxx.xxx.xxx.xxx |
| Public IP | pip-fw-edge-shared-brazilsouth-nat-ssh | xxx.xxx.xxx.xxx |
| Route Table | rt-fw-edge-shared-brazilsouth | Route Table |
| Virtual Network | vnet-fw-edge-shared-brazilsouth | 10.225.0.0/22 |
*Não criamos aqui as VMs (Windows/Linux), mas elas estão na SubNet AzureFirewallSubnet-Trust
Nossas Subnets
AzureFirewallSubnet = 10.225.0.0/24
AzureFirewallManagementSubnet = 10.225.1.0/24
AzureFirewallSubnet-Trust = 10.225.2.0/24
Vamos ao nosso script bash
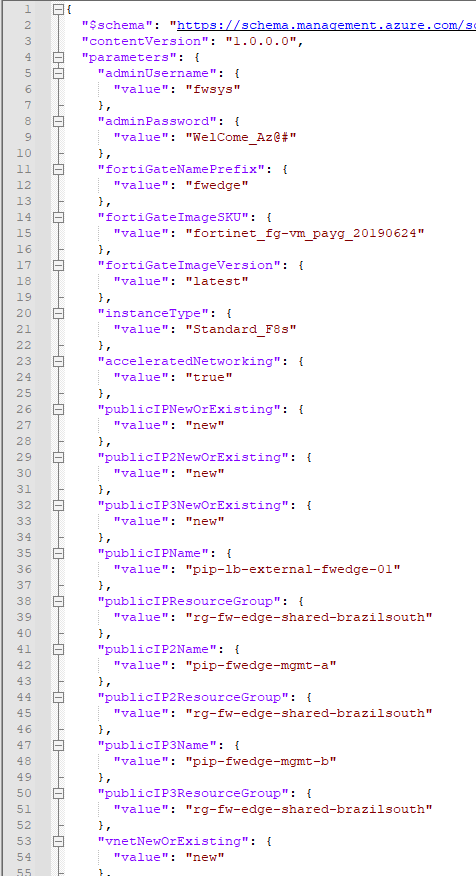
##Declarando variaveis Subscription(obrigatórias)
export Subscription_Name="XXXXX" ###Insira aqui sua subscription Azure
##Declarando variaveis Resource Group(obrigatórias)
export Name_RG_01="rg01"
export Name_RG_02="fw-edge"
export Name_Environment="shared"
export Location_Region="brazilsouth"
export RG_FULL_NAME="${Name_RG_01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"
###Declarando variaveis Firewall (Obrigatório)
export FW_Name01="fw"
##Declarando Variaveis da Vnet (Obrigatório)
export Vnet_Name01="vnet"
export Vnet_FULL_Name="${Vnet_Name01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"
export CIDR="10.225.0.0/22"
##Declarando Variaveis da Subnet (Obrigatório)
export SubnetName="AzureFirewallSubnet"
export Prefix="10.225.0.0/24"
export SubnetName02="AzureFirewallManagementSubnet"
export Prefix02="10.225.1.0/24"
export SubnetName03="AzureFirewallSubnet-Trust"
export Prefix03="10.225.2.0/24"
##Declarando Variaveis SKU/TIER
export SKU="AZFW_VNet"
export TIER="Standard"
export NameIP_01="ifconfig1"
export NameIP_02="nat-ssh"
export NameIP_03="nat-rdp"
##Declarando variaveis de ZONA
export ZONES="1"
##Declarando Variaveis IP Publico
export Public_IP_01="pip"
export Public_IP_02="${Public_IP_01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"-"${Collection_Name03}"
export Public_IP_03="${Public_IP_01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"-"${Collection_Name01}"
export Public_IP_04="${Public_IP_01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"-"${Collection_Name02}"
export SKU_IP="Standard"
export IP_Zone="1"
export AlLocation="Static"
export Tier_IP="Regional"
###Declarando Variaveis de Route Table
export RT_Name01="rt"
export RT_Name02="${RT_Name01}"-"${Name_RG_02}"-"${Name_Environment}"-"${Location_Region}"
export RT_Name03="Default"
export Prefix_Address01="0.0.0.0/0"
###Declarando Variaveis NAT RULE
export Collection_Name01="nat-ssh"
export Collection_Name02="nat-rdp"
export Collection_Name03="nat-out"
export Destination01="10.225.2.4"
###Declarando Variaveis para acesso a internet HTTP/HTTPs
export Colletion_Name_Internet="Acesso_Internet"
##Variaveis TAGs (Não Obrigatório)
export Description="Departamento"
export Value_Description="Redes/Telecom/Segurança/Infraestrutura"
export Cost_Center="Centro de Custo"
export Cost_Center_Value="Redes/Telecom/Segurança/Infraestrutura"
export Support_Description_Description="E-mail Suporte"
export Support_Description_Value="[email protected]"
###Selecionar subscription
az account set --subscription "${Subscription_Name}"
##Criando RG
az group create -n "${RG_FULL_NAME}" -l "${Location_Region}" --tags "${Description}"="${Value_Description}" "${Cost_Center}"="${Cost_Center_Value}" "${Support_Description_Description}"="${Support_Description_Value}"
####Criando Virtual Network (Vnet)
az network vnet create -g "${RG_FULL_NAME}" -n "${Vnet_FULL_Name}" --address-prefix "${CIDR}" -l "${Location_Region}" --tags "${Description}"="${Value_Description}" "${Cost_Center}"="${Cost_Center_Value}" "${Support_Description_Description}"="${Support_Description_Value}"
###Criando Subnet
az network vnet subnet create -g "${RG_FULL_NAME}" --vnet-name "${Vnet_FULL_Name}" -n "${SubnetName}" --address-prefixes "${Prefix}"
az network vnet subnet create -g "${RG_FULL_NAME}" --vnet-name "${Vnet_FULL_Name}" -n "${SubnetName02}" --address-prefixes "${Prefix02}"
az network vnet subnet create -g "${RG_FULL_NAME}" --vnet-name "${Vnet_FULL_Name}" -n "${SubnetName03}" --address-prefixes "${Prefix03}"
###Criando IP Publico
az network public-ip create -n "${Public_IP_02}" -g "${RG_FULL_NAME}" -l "${Location_Region}" --zone "${IP_Zone}" --allocation-method "${AlLocation}" --sku "${SKU_IP}" --tier "${Tier_IP}" --tags "${Description}"="${Value_Description}" "${Cost_Center}"="${Cost_Center_Value}" "${Support_Description_Description}"="${Support_Description_Value}"
az network public-ip create -n "${Public_IP_03}" -g "${RG_FULL_NAME}" -l "${Location_Region}" --zone "${IP_Zone}" --allocation-method "${AlLocation}" --sku "${SKU_IP}" --tier "${Tier_IP}" --tags "${Description}"="${Value_Description}" "${Cost_Center}"="${Cost_Center_Value}" "${Support_Description_Description}"="${Support_Description_Value}"
az network public-ip create -n "${Public_IP_04}" -g "${RG_FULL_NAME}" -l "${Location_Region}" --zone "${IP_Zone}" --allocation-method "${AlLocation}" --sku "${SKU_IP}" --tier "${Tier_IP}" --tags "${Description}"="${Value_Description}" "${Cost_Center}"="${Cost_Center_Value}" "${Support_Description_Description}"="${Support_Description_Value}"
##Criando Azure Firewall
az network firewall create -g "${RG_FULL_NAME}" -n "${Name_RG_02}" --sku "${SKU}" --tier "${TIER}" -z "1" --threat-intel-mode "Alert"
##Associando IP Publico Azure Firewall
az network firewall ip-config create --firewall-name "${Name_RG_02}" --name "${NameIP_01}" --public-ip-address "${Public_IP_02}" -g "${RG_FULL_NAME}" --vnet-name "${Vnet_FULL_Name}"
az network firewall ip-config create --firewall-name "${Name_RG_02}" --name "${NameIP_02}" --public-ip-address "${Public_IP_03}" -g "${RG_FULL_NAME}"
az network firewall ip-config create --firewall-name "${Name_RG_02}" --name "${NameIP_03}" --public-ip-address "${Public_IP_04}" -g "${RG_FULL_NAME}"
###Declarando Variaveis para utilizar IP privado do Azure Firewall
fwprivaddr01="$(az network firewall ip-config list -g "${RG_FULL_NAME}" -f "${Name_RG_02}" --query "[?name=='ifconfig1'].privateIpAddress" --output tsv)"
fwprivaddr02="$(az network public-ip show -g "${RG_FULL_NAME}" -n "${Public_IP_03}" --query "{address: ipAddress}" --output tsv)"
fwprivaddr03="$(az network public-ip show -g "${RG_FULL_NAME}" -n "${Public_IP_04}" --query "{address: ipAddress}" --output tsv)"
###Crando Route Table
az network route-table create -n "${RT_Name02}" -g "${RG_FULL_NAME}" -l "${Location_Region}" --disable-bgp-route-propagation "true"
###Associando Route Table a Subnet
az network vnet subnet update -n "${SubnetName03}" -g "${RG_FULL_NAME}" --vnet-name "${Vnet_FULL_Name}" --address-prefixes "${Prefix03}" --route-table "${RT_Name02}"
###Criando Static Route
az network route-table route create -g "${RG_FULL_NAME}" --name "${RT_Name03}" --route-table-name "${RT_Name02}" --address-prefix "${Prefix_Address01}" --next-hop-type "VirtualAppliance" --next-hop-ip-address $fwprivaddr01
###Criando regra de NAT para acessar uma VM com IP interno 10.255.2.4
az network firewall nat-rule create --collection-name "${Collection_Name}" \
--dest-addr "$fwprivaddr02" --destination-ports "22" --firewall-name "${Name_RG_02}" \
--name "nat-ssh-vm01" --protocols "tcp" -g "${RG_FULL_NAME}" --translated-port "22" \
--action "Dnat" --description "Acesso a VM01" --priority "200" \
--source-addresses "179.xxx.182.42/32" --translated-address "10.225.2.4"
###Criando regra de NAT para acessar uma VM com IP interno 10.255.2.5
az network firewall nat-rule create --collection-name "${Collection_Name02}" \
--dest-addr "$fwprivaddr03" --destination-ports "22" --firewall-name "${Name_RG_02}" \
--name "nat-rdp-vm02" --protocols "tcp" -g "${RG_FULL_NAME}" --translated-port "3389" \
--action "Dnat" --description "Acesso a VM02" --priority "201" \
--source-addresses "179.xxx.182.42/32" --translated-address "10.225.2.5"
###Criando Regras de acesso para Internet (somente HTTP/HTTPs)
az network firewall network-rule create --collection-name "${Colletion_Name_Internet}" \
--destination-ports "80" "443" --firewall-name "${Name_RG_02}" --name "Acesso a Internet" \
--protocols "tcp" --resource-group "${RG_FULL_NAME}" --action "Allow" \
--description "Acesso a Internet rede 10.225.2.0/24" --dest-addr "0.0.0.0/0" \
--priority "200" --source-addresses "10.225.2.0/24"
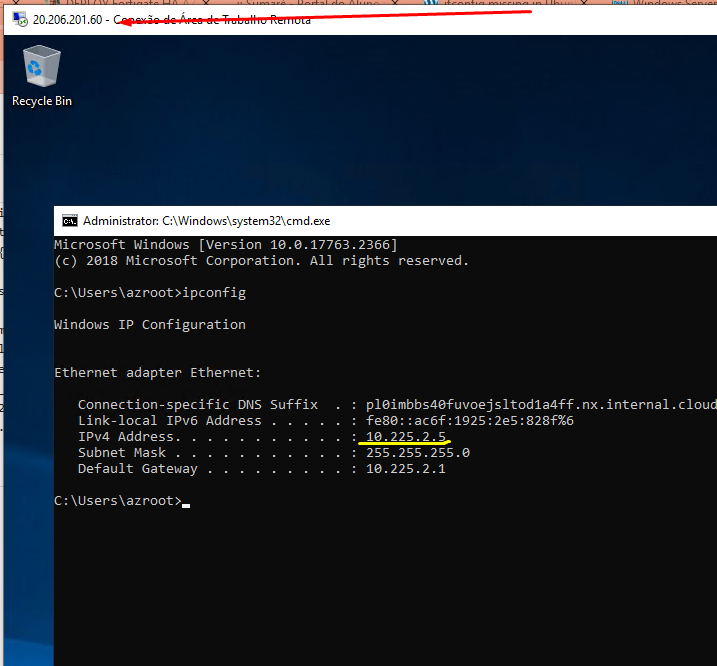
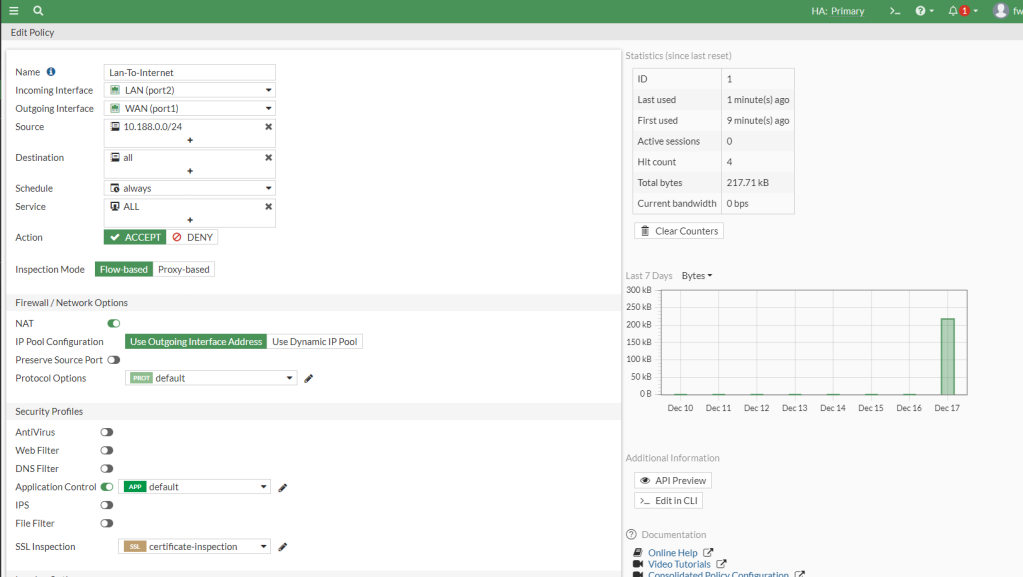
###Fim do scriptVemos a VM Windows
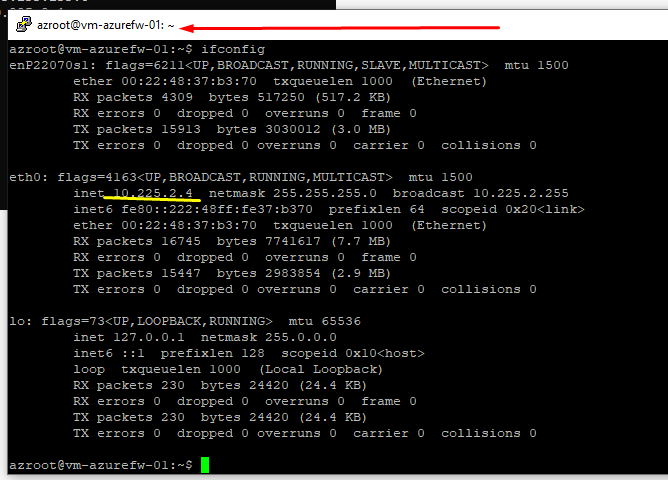
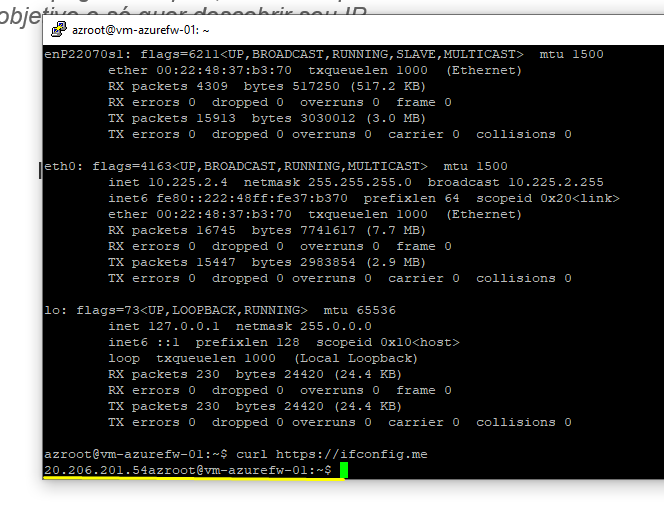
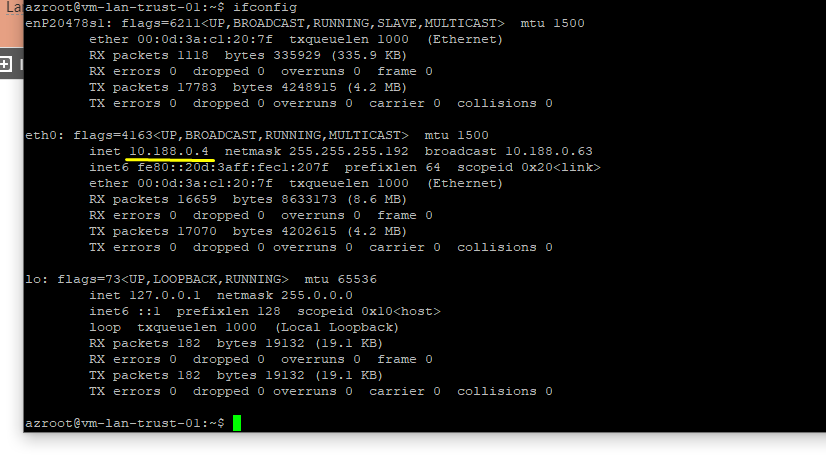
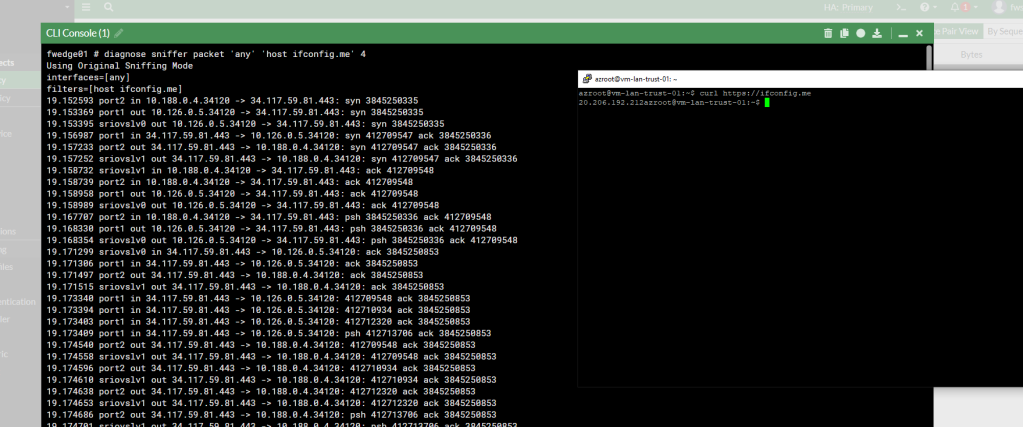
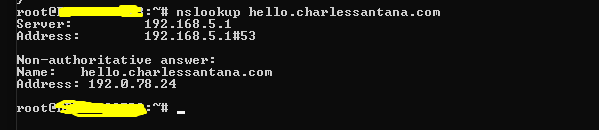
Vemos a VM Linux
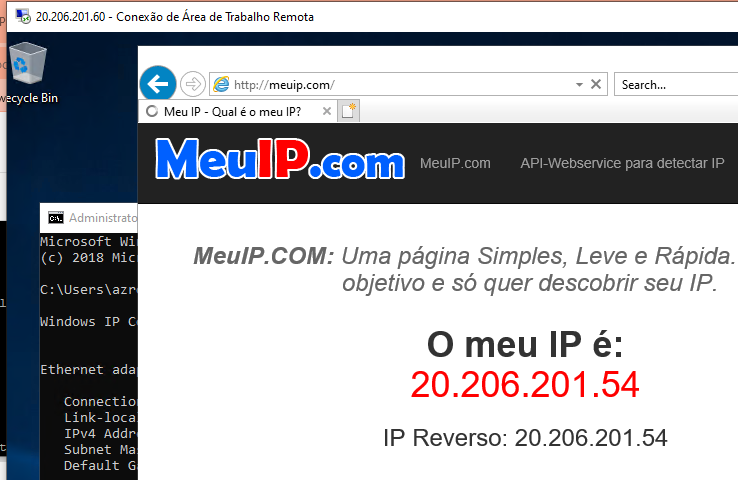
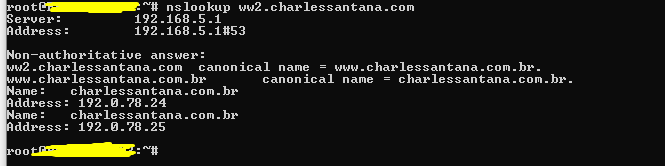
Agora vemos o NAT OutBound para acesso a internet
Windows (mesmo IP cadastrado no Firewall)
Linux (mesmo IP cadastrado no Firewall)
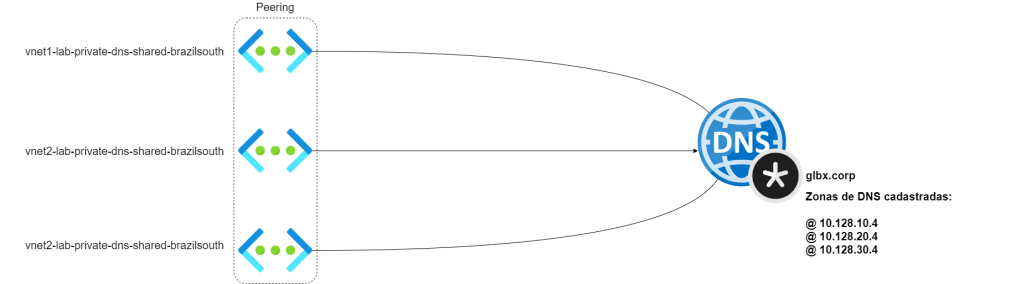
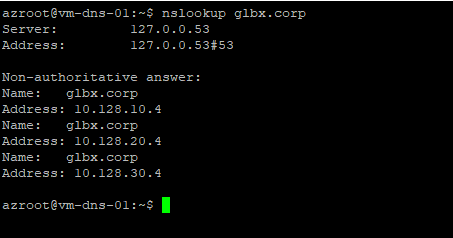
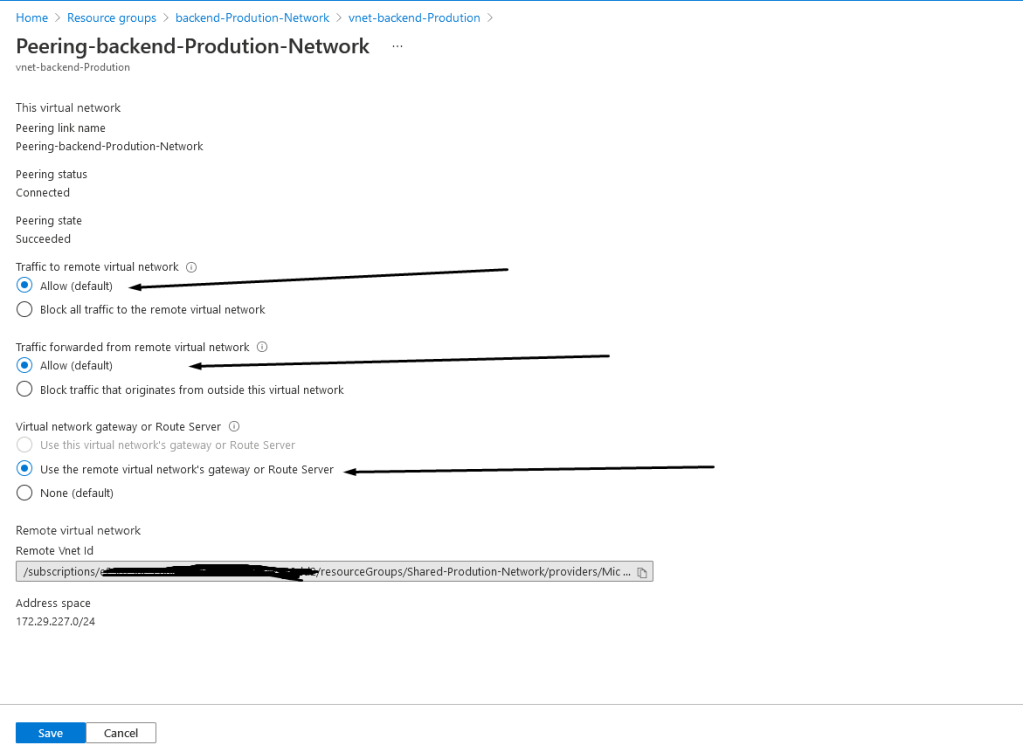
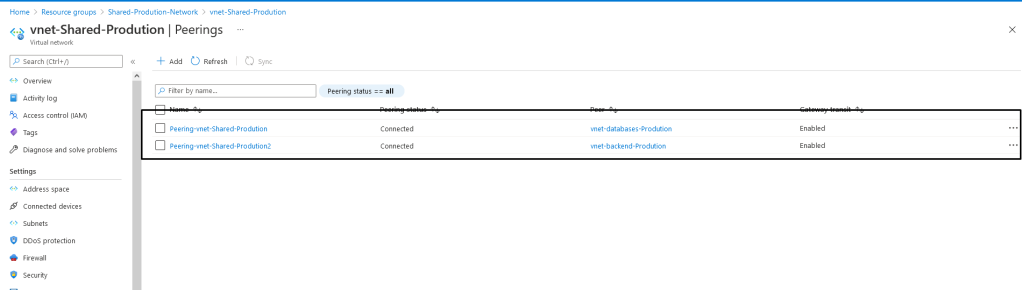
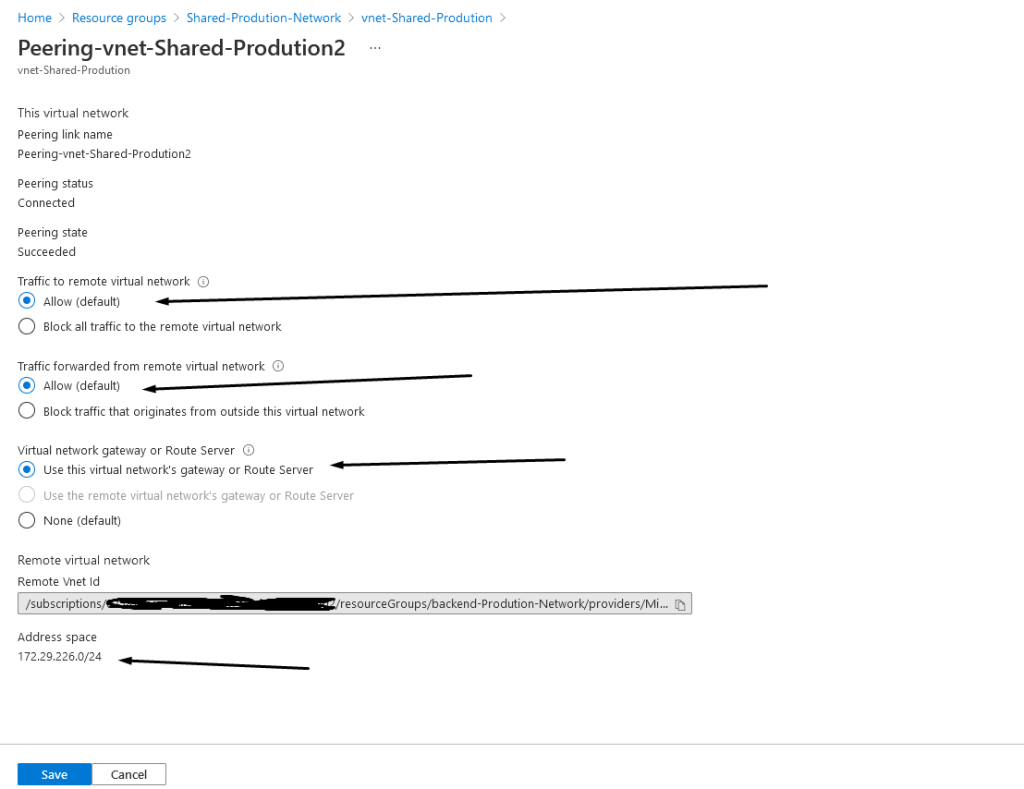
Em cima desta topologia podemos criar varias Vnets com peering e fazer do azure firewall nossa BORDA (EDGE), tudo contralado em um só lugar.
Seja Feliz!!!!

Você precisa fazer login para comentar.